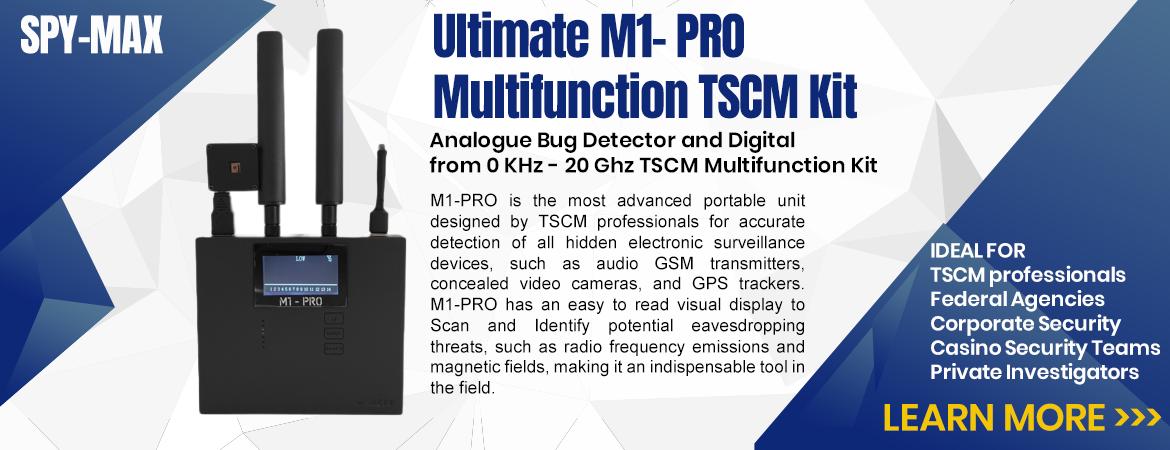
Key TSCM Products and Features:
-
Advanced Detection: Our devices can identify hidden surveillance devices operating across a wide range of frequencies, including analog and digital signals, up to 20 GHz.
-
Specialized Antennas: Equipped with antennas for laser listening device and infrared microphone detection, thermal antenna for heat detection, Audio Vox bug alarm clock antenna, GPS alarm clock antenna, and more.
-
Distance Measurement: Measure the distance of detected signals down to the centimeter, enhancing your precision.
-
Micro Camera Detection: Our probes can detect micro cameras, even when they are switched off and utilizing infrared technology.
-
User-Friendly App: Manage and control your TSCM equipment through our intuitive mobile application.
Our TSCM solutions encompass cutting-edge technology and expertise, making them the top choice for professionals worldwide. Whether you need to safeguard corporate secrets, protect high-net-worth individuals, or ensure executive confidentiality, our TSCM equipment provides unparalleled security.
Choose our TSCM products to take proactive measures against espionage threats and maintain the utmost privacy and security for your clients. Contact us today to learn more about our wholesale counter-surveillance solutions.
What Is Counter Surveillance? Who Is Watching Who?
There's something important to be said for knowing whose eyes could be on your personal, private affairs at any given time. It may be a jealous present-day romantic partner or a vindictive, stalking ex-spouse. More employers than ever keep quiet tabs on their employees to assess their character and loyalty when they believe their superiors aren't watching. Of course, privacy is violated every day everywhere by nosy neighbors looking for nothing more than some juicy gossip.
Counter surveillance is your trump card that turns the tables on prying eyes and ears lurking for whatever coveted intelligence they can quietly pirate. It's time to match unwanted observers tech-for-tech.
Counter Surveillance Equipment For Every Situation
A fair majority of counter surveillance depends upon sophisticated radio frequency (RF) and/or infrared (IR) detection via either devices dedicated to detecting a single kind of device, such as hidden cameras or audio bugs, or counter surveillance devices designed with versatility to expose several kinds of equipment. It is not uncommon for an unauthorized hidden camera to placed in public areas. Many portable camera-finding counter surveillance devices key on laser or RF signatures to spot covert recording devices, not unlike the way wide-band RF detection equipment points out listening devices.
As sophisticated as cell phone technology has become in less than 20 years, equally advanced portable RF detectors have become commonplace tools in prisons, government institutions, workplaces and among private citizens to root out unwanted eavesdroppers. There could even be hidden GPS tracking devices cleverly inside small objects or even in your car giving a prying individual exact location of your whereabouts. GPS detectors are valuable assets in their own rights for businesses suspicious of shipments being tracked for interception or generally anyone wary that their movements are being quietly documented and patterned. Meanwhile, acoustic noise detectors will pick up on individuals bold enough to personally peer in unseen on personal affairs while wiretap detectors ensure that one-on-one phone conversations aren't invaded by secret surveillance.
Finally, there's no understating the value of protecting the personal data logged by your personal electronic devices. Criminals the world over use RFID scanning to infiltrate security measures and steal private information as simply as lifting a billfold. Devices and wallets with RFID-blocking hardware keeps a secure wall around your digital data at all times, wherever you go.
Don't Wait Until You've Been Violated. Prevention Is The Smartest Action
The cold, hard truth: becoming wise to covert surveillance after the fact may stop a bleed of information, but likely far too late to ever shove the genie back into the bottle. Once your most private and personal secrets are exposed, they're out there for good. Information can't be "un-learned". While you may benefit from admissible and undeniable legal proof of record, any recompense from a court of law is unlikely to meaningfully undo damage already done.
Counter surveillance equipment can subvert the kind of secret personal sabotage that destroys careers, poisons relationships and marriages, and can quickly lead to damning blackmail, extortion and crippling identity theft. However, these counter surveillance devices achieve their maximum benefits only when employed a step ahead of saboteurs and spies who direct their prying ears and eyes where they aren't welcome.
Our products are the exact same counter surveillance equipment used by law enforcement, FBI and PI's when doing sweeps of businesses or homes. The difference is hiring a PI will cost thousands to perform the same sweeps that you can do yourself daily for a fraction of the cost.
Professional TSCM tools for lawful, defensive privacy assessments. Detect and help locate potential surveillance devices in spaces you own or manage. These products do not intercept or interfere with communications.